第7章 专业英语
★DOM is a platform- and language- (1)API that allows programs and scripts to dynamically access and update the content, structure and style of WWW documents(currently, definitions for HTML and XML documents are part of the specification). The document can be further processed and the results of that processing can be incorporated back into the presented (2) . DOM is a (3) -based API to documents, which requires the whole document to be represented in (4) while processing it. A simpler alternative to DOM is the event-based SAX, which can be used to process very large (5) documents that do not fit into the memory available for processing.
(1)A.specific
B.neutral
C.contained
D.related
(2)A.text
B.image
C.page
D.graphic
(3)A.table
B.tree
C.control
D.event
(4)A.document
B.processor
C.disc
D.memory
(5)A.XML
B.HTML
C.script
D.Web
★Melissa and LoveLetter made use of the trust that exists between friends or colleagues. Imagine receiving an (6) from a friend who asks you to open it. This is what happens with Melissa and several other similar email (7) . Upon running, such worms usually proceed to send themselves out to email addresses from the victim's address book, previous emails, web pages (8) .
As administrators seek to block dangerous email attachments through the recognition of well-known (9) , virus writers use other extensions to circumvent such protection. Executable(.exe)files are renamed to .bat and .cmd plus a whole list of other extensions and will still run and successfully infect target users.
Frequently, hackers try to penetrate networks by sending an attachment that looks like a flash movie, which, while displaying some cute animation, simultaneously runs commands in the background to steal your passwords and give the (10) access to your network.
(6)A.attachment
B.packet
C.datagram
D.message
(7)A.virtual
B.virus
C.worms
D.bacteria
(8)A.memory
B.caches
C.ports
D.registers
(9)A.names
B.cookies
C.software
D.extensions
(10)A.cracker
B.user
C.customer
D.client
★MIDI enables people to use (11) computers and electronic musical instruments. There are actually three components to MIDI, the communications " (12) ", the Hardware interface and a distribution (13) called "Standard MIDI Files". In the context of the WWW, the most interesting component is the (14) Format. In principle, MIDI files contain sequences of MIDI Protocol messages. However, when MIDI Protocol (15) are stored in MIDI files, the events are also time-stamped for playback in the proper sequence. Music delivered by MIDI files is the most common use of MIDI today.
(11)A.personal
B.electronic
C.multimedia
D.network
(12)A.device
B.protocol
C.network
D.controller
(13)A.format
B.text
C.wave
D.center
(14)A.Video
B.Faxmail
C.Graphic
D.Audio
(15)A.messages
B.packets
C.frame
D.information
★Certificates are (16) documents attesting to the (17) of a public key to an individual or other entity. They allow verification of the claim that a given public key does in fact belong to a given individual. Certificates help prevent someone from using a phony key to (18) someone else. In their simplest form, Certificates contain a public key and a name. As commonly used, a Certificate also contains an (19) date, the name of the CA that issued the Certificate, a serial number, and perhaps other information. Most importantly, it contains the digital (20) of the certificate issuer. The most widely accepted format for certificates is X.509, thus, Certificates can be read or written by any application complying with X.509.
(16)A.text
B.data
C.digital
D.structured
(17)A.connecting
B.binding
C.composing
D.conducting
(18)A.impersonate
B.personate
C.damage
D.control
(19)A.communication
B.computation
C.expectation
D.expiration
(20)A.signature
B.mark
C.stamp
D.hypertext
★Originally introduced by Netscape Communications, (21) are a general mechanism which HTTP Server side applications, such as CGI (22) , can use to both store and retrieve information on the HTTP (23) side of the connection. Basically, Cookies can be used to compensate for the (24) nature of HTTP. The addition of a simple, persistent, client-side state significantly extends the capabilities of WWW-based (25) .
(21)A.Browsers
B.Cookies
C.Connections
D.Scripts
(22)A.graphics
B.processes
C.scripts
D.texts
(23)A.Client
B.Editor
C.Creator
D.Server
(24)A.fixed
B.flexible
C.stable
D.stateless
(25)A.programs
B.applications
C.frameworks
D.constrains
★WebSQL is a SQL-like (26) language for extracting information from the web.Its capabilities for performing navigation of web (27) make it a useful tool for automating several web-related tasks that require the systematic processing of either all the links in a (28) , all the pages that can be reached from a given URL through (29) that match a pattern, or a combination of both. WebSQL also provides transparent access to index servers that can be queried via the Common (30) Interface.
(26)A.query
B.transaction
C.communication
D.programming
(27)A.browsers
B.servers
C.hypertexts
D.clients
(28)A.hypertext
B.page
C.protocol
D.operation
(29)A.paths
B.chips
C.tools
D.directories
(30)A.Router
B.Device
C.Computer
D.Gateway
★Every valid character in a computer that uses even (31) must always have an even number of 1 bits.
(31)A.parity
B.check
C.test
D.compare
★The maximum number of data that can be expressed by 8 bits is (32) .
(32)A.64
B.128
C.255
D.256
★Integration (33) is the process of verifying that the components of a system work together as described in the program design and system design specifications.
(33)A.trying
B.testing
C.checking
D.coding
★GIF files are limited to a maximum of 8 bits/pixel, it simply means that no more than 256 colors are allowed in (34) .
(34)A.an image
B.a file
C.a window
D.a page
★Computer (35) is a complex consisting of two or more connected computing units, it is used for the purpose of data communication and resource sharing.
(35)A.storage
B.device
C.processor
D.network
★NAC's(Network Access Control)role is to restrict network access to only compliant endpoints and (36) users. However, NAC is not a complete LAN (37) solution; additional proactive and (38) security measures must be implemente D.Nevis is the first and only comprehensive LAN security solution that combines deep security processing of every packet at 10Gbps, ensuring a high level of security plus application availability and performance. Nevis integrates NAC as the first line of LAN security (39) . In addition to NAC, enterprises need to implement role-based network access control as well as critical proactive security measures — real-time, multilevel (40) inspection and microsecond threat containment.
(36)A.automated
B.distinguished
C.authenticated
D.destructed
(37)A.crisis
B.security
C.favorable
D.excellent
(38)A.constructive
B.reductive
C.reactive
D.productive
(39)A.defense
B.intrusion
C.inbreak
D.protection
(40)A.port
B.connection
C.threat
D.insurance
★Which of the following elements can be called the key element of a computer? (41)
(41)A.printer
B.CPU
C.mouse
D.keyboard
★The (42) has several major components, including the system kernel, a memory management system, the file system manager, device drivers, and the system libraries.
(42)A.application
B.information system
C.operating system
D.iterative
★Which of the following is not part of the quality assurance process? (43)
(43)A.Operational definitions
B.Quality policy
C.Quality audits
D.Quality improvement
★Which of the following is not part of a modern quality management concept? (44)
(44)A.Performance standard is zero defects
B.Quality must be inspected in
C.85% of failures occur because of the process, not the worker
D.Quality is a 4 cycle process – plan/do/check/act
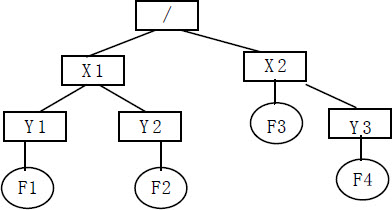
★Each box is an activity; the number it contains is the duration of the activity in days. The duration of the critical path is (45) .
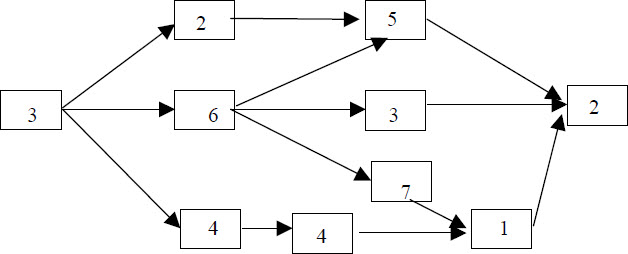
(45)A.16 days
B.14 days
C.19 days
D.20 days
★Consumption of the total life-cycle effort in software maintenance is (46) that in software development.
(46)A.less than
B.larger than
C.equal or less than
D.equal or larger than
★The process of software development doesn't include (47) .
(47)A.verification function
B.writing code
C.management function
D.validation function
★A well-designed system should be (48) .
①easily understood
②reliable
③straightforward to implement
④straightforward to maintain
(48)A.①②
B.①③④
C.②③④
D.①②③④
★Maintenance activities include (49) .
①making enhancements to software products
②developing a new software product
③correcting problems
④adapting products to new environments
(49)A.①②
B.①③④
C.②③④
D.①②③④
★A quality assurance team should be (50) .
①associated with any particular development group
②depended upon any particular development group
③responsible for reporting directly to management
④in-depended upon any particular development group
(50)A.①②
B.②③
C.③④
D.①②③④
★In software engineering and systems engineering, (51) is a description of a system's behavior as it responds to a request that originates from outside of that system.
(51)A.black box
B.business rule
C.use case
D.traceability matrix
★The standard(IEEE 802)format for printing (52) in human-friendly form is six groups of two hexadecimal digits, separated by hyphens(-)or colons(:), in transmission order, e.g. 01-23-45-67-89-ab, 01:23:45:67:89:ab.This form is also commonly used for EUI-64.
(52)A.hard disk logical block address
B.IP address
C.mail address
D.MAC address
★ (53) operate by distributing a workload evenly over multiple back end nodes. Typically the cluster will be configured with multiple redundant load-balancing front ends.
(53)A.High-availability clusters
B.Load-balancing clusters
C.Grid computing
D.Cloud Computing
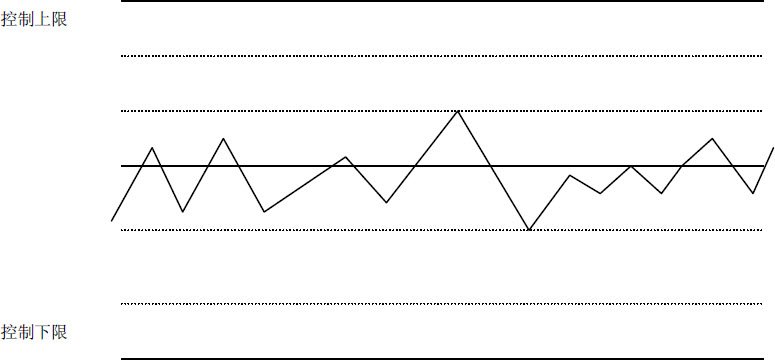
★A PM wanted to show management,visually, how quality controls were affecting processes. The best tool to accomplish this is (54) .
(54)A.Diagrams
B.Histograms
C.Flowcharts
D.Control charts
★Configuration management is the process of managing change in hardware, software, firmware, documentation, measurements, etc.As change requires an initial state and next state, the marking of significant states within a series of several changes becomes important. The identification of significant states within the revision history of a configuration item is the central purpose of (55) identification.
(55)A.baseline
B.value
C.cost
D.control
★The connection between two networks to form an internet is handled by a machine known as a (56) .
(56)A.bridge
B.client
C.router
D.switch
★One tool that is useful during both analysis and design is the (57) ,which is a pictorial representation of the items of information(entities)within the system and the relationships between these pieces of information.
(57)A.data dictionary
B.dataflow diagram
C.use case diagram
D.entity-relationship diagram
★ (58) is one of the techniques used for estimating activity durations.
(58)A.Analogous Estimating
B.Precedence Diagramming Method(PDM)
C.Dependency Determination
D.Schedule network Templates
★Project Time Management includes the processes required to manage timely completion of the project, these processes interact with each other. (59) is following the process- Estimate Activity Durations.
(59)A.Develop Schedule
B.Estimate Activity Resources
C.Define Activities
D.Sequence Activities
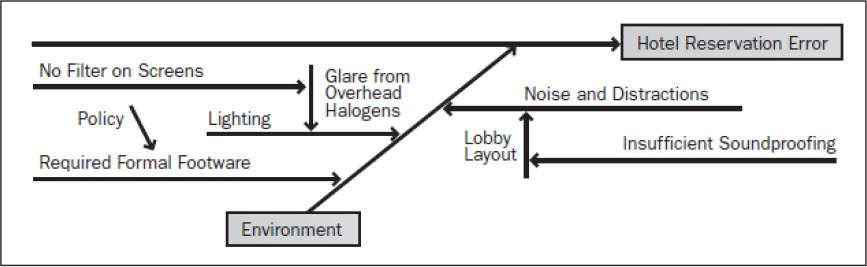
★ (60) is not the tool name for quality controlling used in the figure below.
(60)A.Cause and Effect Diagrams
B.Ishikawa Diagrams
C.Fishbone Diagrams
D.Scatter Diagram
★Which of the following would require real-time processing? (61)
(61)A.Playing a computer game
B.Executing a program that predicts the state of economy
C.Printing labels
D.Listening the music
★ (62) is a client/server protocol for transferring files across the Internet.
(62)A.POP3
B.IMAP
C.FTP
D.HTTP
★Tool for defining activities is (63) .
(63)A.Dependency Determination
B.Precedence Diagramming method
C.Rolling Wave Planning
D.Schedule network Templates
★Changes often happen in (64) .
(64)A.Initiating Process
B.Executing Process
C.Planning Process
D.Closing Process
★Which of the following is not part of the change-management process of IT supervisor? (65)
(65)A.change analyses
B.change evaluation
C.change acquisition
D.change executing
★10BaseT is an Ethernet LAN term meaning a maximum transfer rate of 10 Mbps that uses baseband signaling and twisted pair cabling. A 10BaseT Ethernet LAN has a (66) topology.
(66)A.star
B.ring
C.bus
D.none of the above
★A work breakdown structure(WBS)is a tool used to define and group a project's discrete work elements in a way that helps organize and define the total work scope of the project. A WBS is most useful for (67) .
(67)A.identifying individual tasks for a project
B.scheduling the start of tasks
C.scheduling the end of tasks
D.determining potential delays
★Sub-contractors should obey the contractor in information system project. When censoring sub-contractors, the supervisor mostly concerns about (68) .
(68)A.Amount of subcontract
B.qualifications and abilities of sub-contractors
C.responsibilities and obligations of sub-contractors
D.the contents of the subcontract
★You are a project manager for a small project. Your project was budgeted for ¥500,000 over a six-week perio D.As of today, you've spent ¥260,000 of your budget to complete work that you originally expected to cost ¥280,000. According to your schedule, you should have spent ¥300,000 by this point. Based on these circumstances, your project could be best described as (69) .
(69)A.ahead of schedule
B.behind schedule
C.on schedule
D.having not enough information provided
★Which statement about the preliminary design stage of a software development project is true? (70) .
(70)A.The preliminary design is an internal document used only by programmers
B.The preliminary design is the result of mapping product requirements into software and hardware functions
C.The preliminary design of the product comes from the requirement specification
D.The developers produce the preliminary design by defining the software structure in enough detail to permit coding
★The prototyping method is a dynamic design processes,which requires people who use prototyping method to have the following capability of (71) .
(71)A.proficient program expertise
B.immediately acquire requirement
C.coordinata&organize eloquently
D.handle tools smartly
★TCP(Transmission Control Protocol)was specifically designed to provide a reliable end-to-end byte stream over a(n) (72) .
(72)A.IP address
B.reliable network
C.socket
D.unreliable internetwork
★A 10BaseT Ethernet LAN has (73) .
(73)A.a star topology
B.a ring topology
C.a bus topology
D.a linear topology
★Maintenance activities do not include (74) .
(74)A.making enhancements to software products
B.developing a new software product
C.correcting problems
D.adapting products to new environments
★When a bridge transmits an Ethernet frame, the Ethernet frame- has (75) .
(75)A.the broadcast address for the its source address
B.the bridge's LAN address for its destination address
C.the bridge's LAN address for its source address
D.none of the above
★A (76) is used to communicate with another computer over telephone lines.
(76)A.keyboard
B.modem
C.mouse
D.printer
★The basic unit of measure in a computer system is the (77) . It is the smallest unit in computing. There are some other measures in a computer, such as Kilobyte, Megabyte, Gigabyte and so on.
(77)A.Kilobyte
B.Bit
C.Gigabyte
D.Megabyte
★Stack is quite simple. Many computer systems have stacks built into their circuitry. They also have machine-level instructions to operate the hardware stack. Stack is (78) in computer systems.
(78)A.useless
B.not important
C.simple but important
D.too simple to be useful
★Since RAM is only active when the computer is on, your computer uses disk to store information even when the computer is off. Which of the following is true? (79)
(79)A.When your computer is on, only RAM is used to store information.
B.When your computer is on, only disk drives are used to store information.
C.When your computer is off, only RAM is used to store information.
D.When your computer is off, only disk drives are used to store information.
★ (80) Development is a structured design methodology that proceeds in a sequence from one phase to the next.
(80)A.Waterfall
B.Phased
C.Prototyping
D.Parallel
★To determine wherher or not the employee correctly understands the message,the project manager needs to (81) .
(81)A.reduce the filtering
B.eliminate barriers
C.obtain feedback
D.use more than one medium
★Performing (82) involves monitoring specific project results to determine if they comply with relevant quality srandards and identifying ways to eliminate causes of unsatisfactory results.
(82)A.quality planning
B.quality assurance
C.quality performance
D.quality control
★Which of the following is not an input to quality planning? (83) .
(83)A.scope statement
B.rigulations
C.work results
D.standards
★Models drawn by the system analysts during the process of the srtuctured amalysis are (84) .
(84)A.PERTs
B.EMV
C.UMLs
D.DFDs
★Which is the second layer from the bottom in open system Interconnection Reference Model? (85) .
(85)A.Application
B.Data Link
C.Network
D.Session

 在线客服
在线客服
共有0条评论 网友评论
暂无评论,快来抢沙发吧!